Threat hunting in Data Explorer
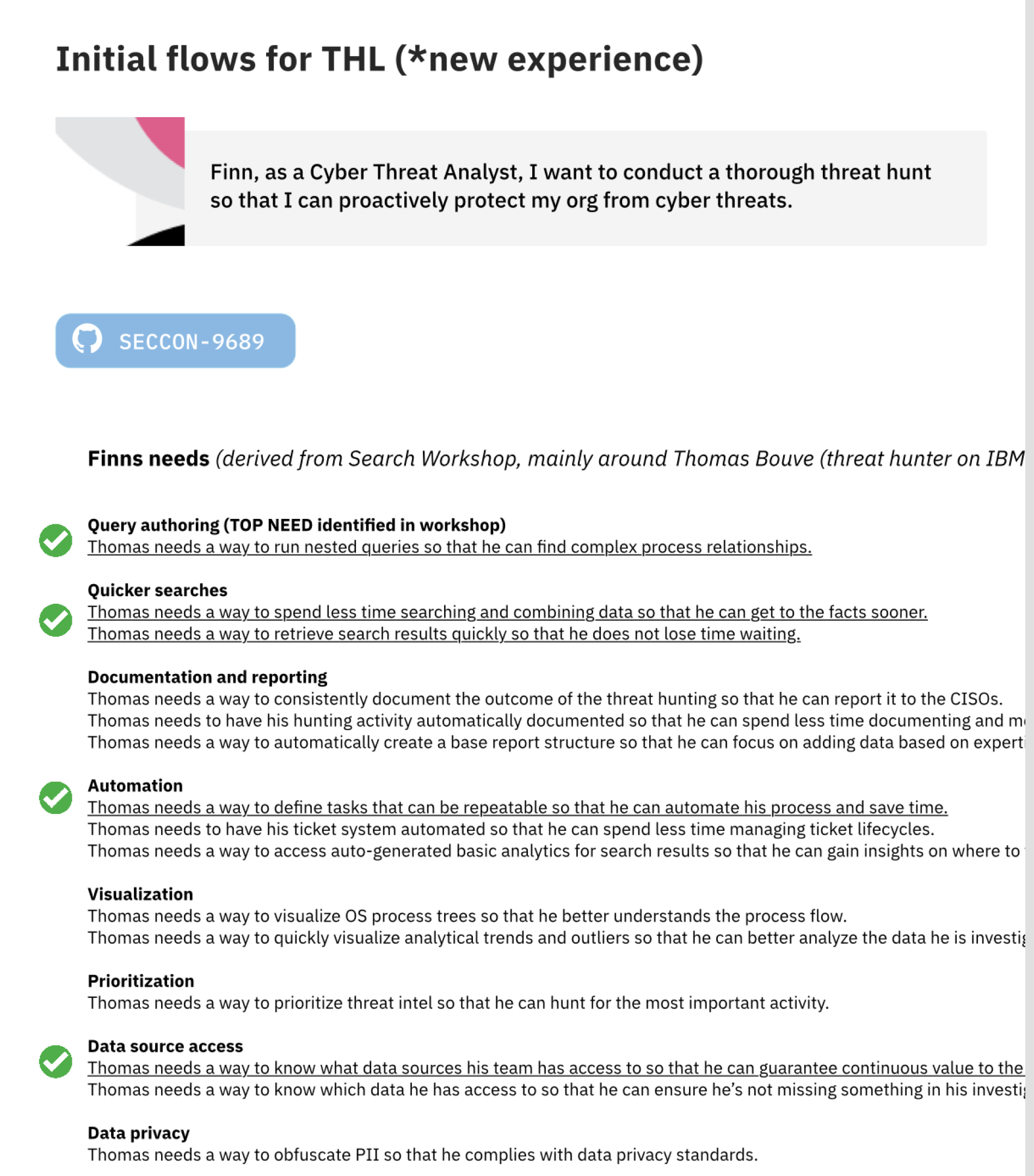
When research revealed that we were missing a key market segment, security analysts doing threat hunting, I simplified their experience by removing the need to learn proprietary query languages and by providing templates that guide analysts on their hunts. Reducing the complexity reduced the time it takes for users to find the necessary evidence to prove or disprove their hypotheses.
Skills used
Leadership, UX design, UI design, UX research, prototyping
Background
Security analysts can only spend 30% of their time proactively searching for unknown threats. That amount of time isn’t always enough to complete a threat hunt. In addition, threat hunting tools are often cumbersome and require analysts to learn complex query languages to sift through impossibly large amounts of raw data.