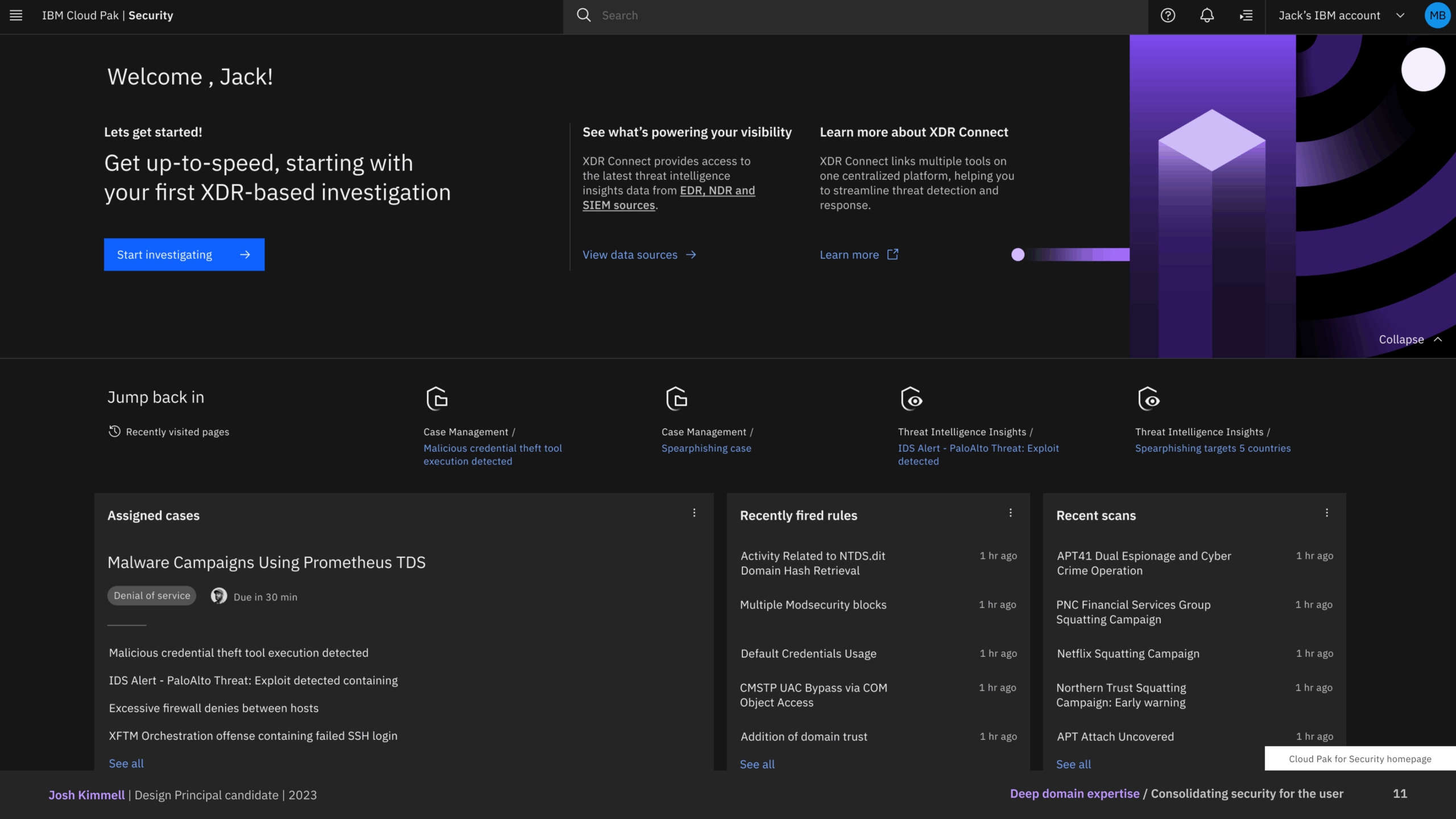
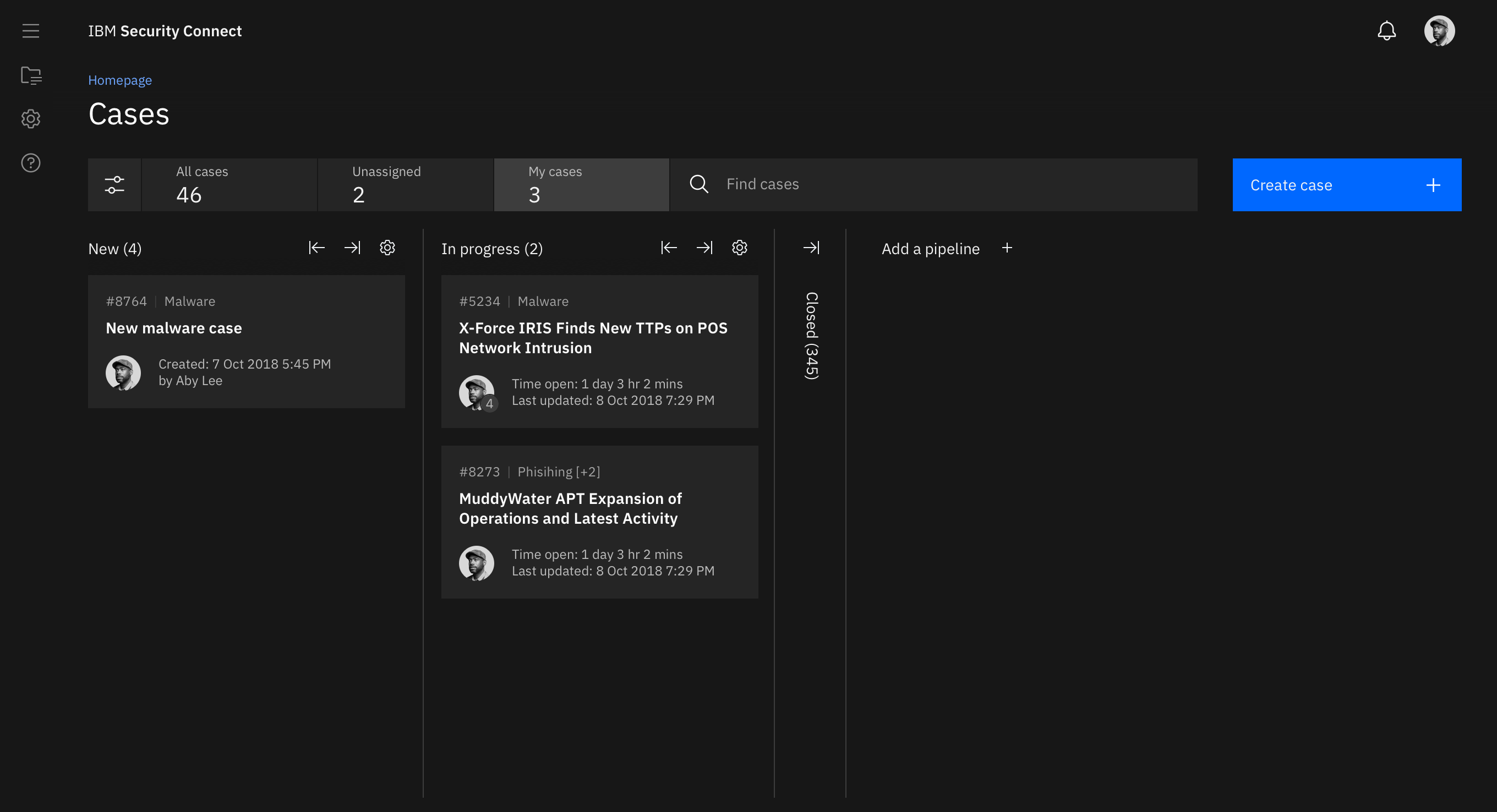
Cloud Pak for Security
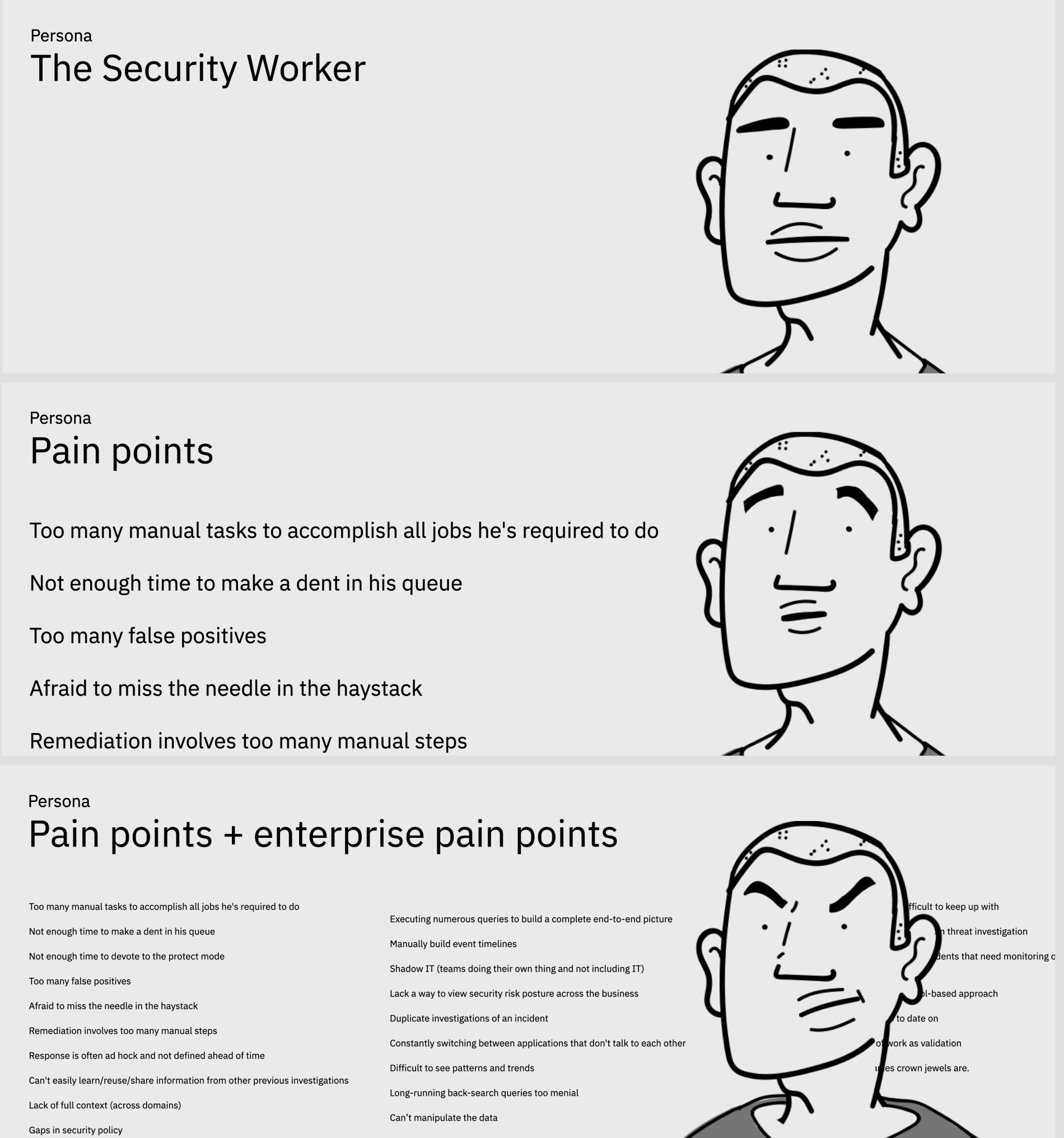
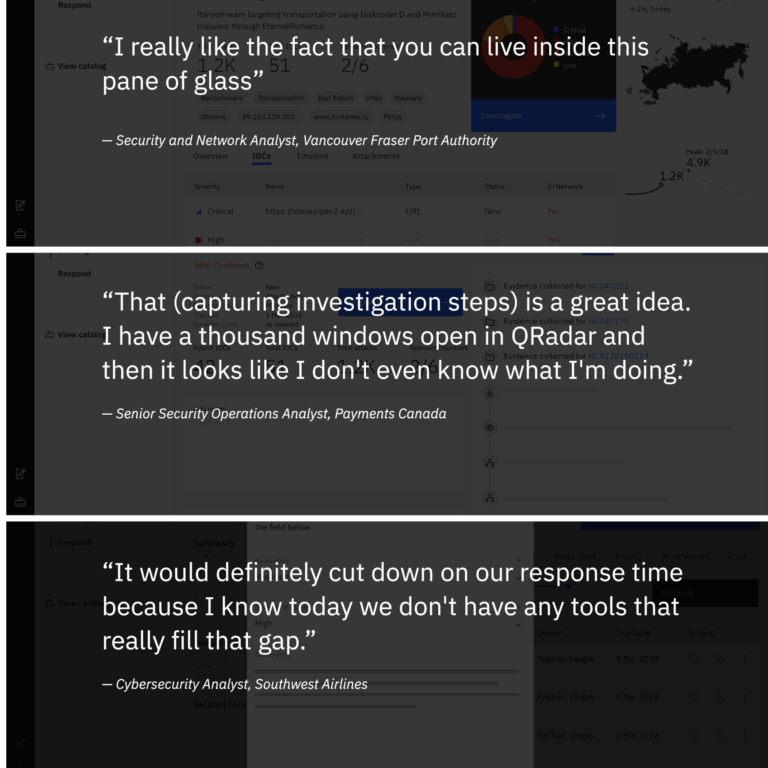
When we kicked off the “Security platform” project in 2017, I was fairly new to the cybersecurity domain. During onboarding, I took the requisite SOC analyst and incident responder trainings and was continuously researching industry trends and learning more about security operations. With this knowledge coupled with my expertise in UX principles, I was able to deliver an experience that enabled security professionals to quickly integrate their existing security tools, generate deeper insights into threats, orchestrate actions, and automate responses—all while leaving their data where it is.
Skills used
Leadership, UX design, UI design, prototyping, project management, UX research, workshop facilitation
Background
In 2017, IBM Security had over 100 disparate and disconnected security products spread over many teams. Security professionals had similar problems with disconnected data and too many security tools that didn’t work together.